No Password Manager vs Password Manager
Nowadays, web users have registered themselves on many websites. Each website asks for a new password that should be hard to guess and easy to remember. However, it turns out to be a pretty difficult task.
If you don't really care about having many passwords, you probably end up reusing the same password over and over because it's better than defining unique passwords that you won't remember at some point. Not to mention that you'd probably store them in a spreadsheet file in your home folder.
Well, let's discuss how to securely deal with passwords by comparing the following approaches:
- No Password Manager
- Online Password Manager
- Offline Password Manager
Security Principles for Managing Passwords
First of all, to securely handle passwords, I've listed five ideal and main principles that we should keep in mind, no matter which option you choose:
- Passwords must be complex, i.e., hard to guess.
- Passwords must be unique for every account you have.
- Passwords must be stored securely.
- Passwords must be transmitted securely, e.g., from your password vault to the web page or from your password vault to your mobile device.
- The process of managing passwords must be easy to use, otherwise, it won't stick.
No Password Manager
This approach includes managing your passwords using either paper or digital formats. Did I say paper? Yes. The more you know about attacks and encryption, the more you start loving paper.
1. Passwords must be complex: Generating strong passwords without password managers is a challenging task because we're biased in our generation pattern, but it still should not be hard to generate a strong password that you won't need to remember. In this topic, you can just randomly press the keys of your keyboard using SHIFT on some keys and not on others, plus adding numbers to it until you reach a desirable size, e.g., 20 characters.
2. Passwords must be unique for every account you have: Just repeat the generation process for each account, thus you'll have different complex passwords for every account. The problem will be accessing them, but keep reading :)
3. Passwords must be stored securely: That's the tough part. If you're using paper, there is the risk of being robbed or someone sneaking into your room and photographing all your passwords, just like a credit card.
If you're using a digital method, you can choose to store it in a file like a spreadsheet, but chances are that you don't have full disk encryption, so a backup of your notebook will be enough to dump all your passwords. A better option is to store all your passwords in your email provider. For example, if you use Gmail, storing them in a draft is better. Why? Because when you forget a password, if you still have access to your email, you can reset it, thus your password is as strong as your email provider account access. Make sure to enable two-step verification on your provider for enhanced security.
But what's the problem with this approach? Drafts may be cached in your browser, allowing someone to back up your hard drive again, or if you have synchronized your mobile phone to access your email (I bet 99% of people do this), you'll have another copy of your passwords cached on your mobile phone. Your email provider will have access to all your passwords, but seriously, Google has much more valuable data than your passwords to begin with. Not to mention that it's not shoulder-surfing resistant. You can't log in to any service when sharing your screen or when someone is behind you, as they would be able to see your passwords.
4. Passwords must be transmitted securely: You don't need to remember your passwords, but you have to move them from your vault (be it encrypted or not) to the login page. It turns out that you'll probably copy and paste them, but beware that other programs may access your clipboard. Or a malware infection may dump your memory or log your keystrokes, thus defeating this whole password management process. You need to make sure to empty your clipboard after pasting the password. Just copy anything else, ideally even before submitting the login form. For mobile devices, you need to type your password again while looking at where they're stored on your computer or look in your draft folder in your email app.
5. The process of managing passwords must be easy to use: In general, it's just switching tabs and copying/pasting passwords. But it requires you to have continuous access to your email account, and it's really a problem when logging in using an untrusted machine.
Online Password Manager
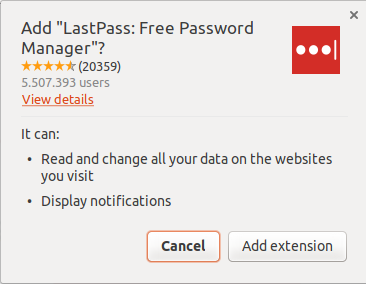
I'm using LastPass, a free service, for this category of online password managers. An online password manager is actually a mix of an offline password manager with online capabilities to share passwords and synchronize them across multiple devices. To sign up, I went to the LastPass website and was prompted to install their browser extension:
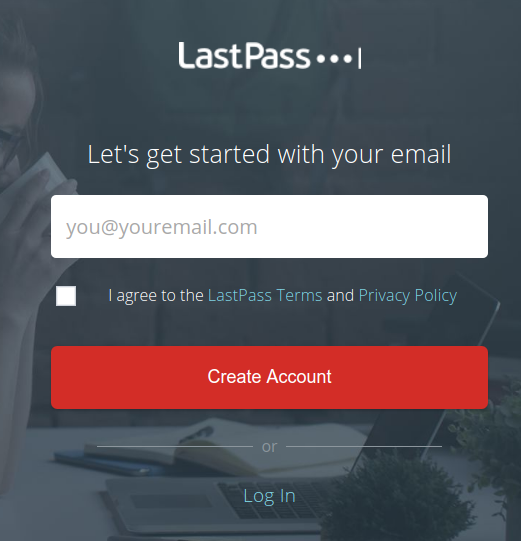
Then, every action afterwards happens within this extension. The URL starts with chrome-extension://, where I'm asked to sign up. It's similar to having installed an app on my mobile phone:
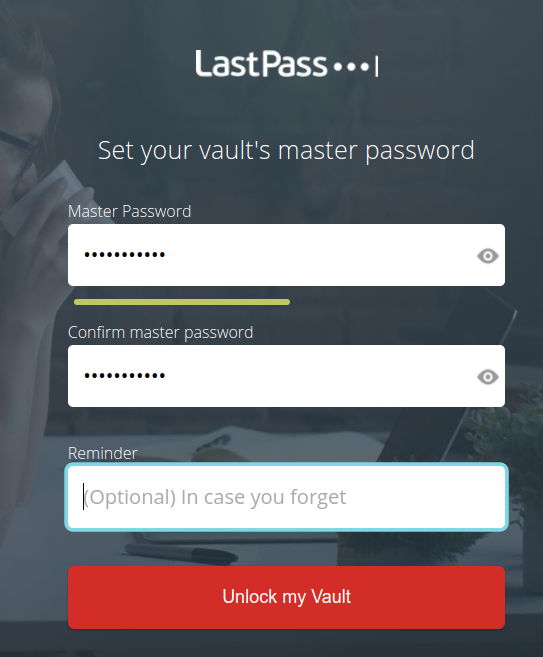
And on the next page, I'm asked to set up "the last pass" I will need to remember, the so-called "master password":
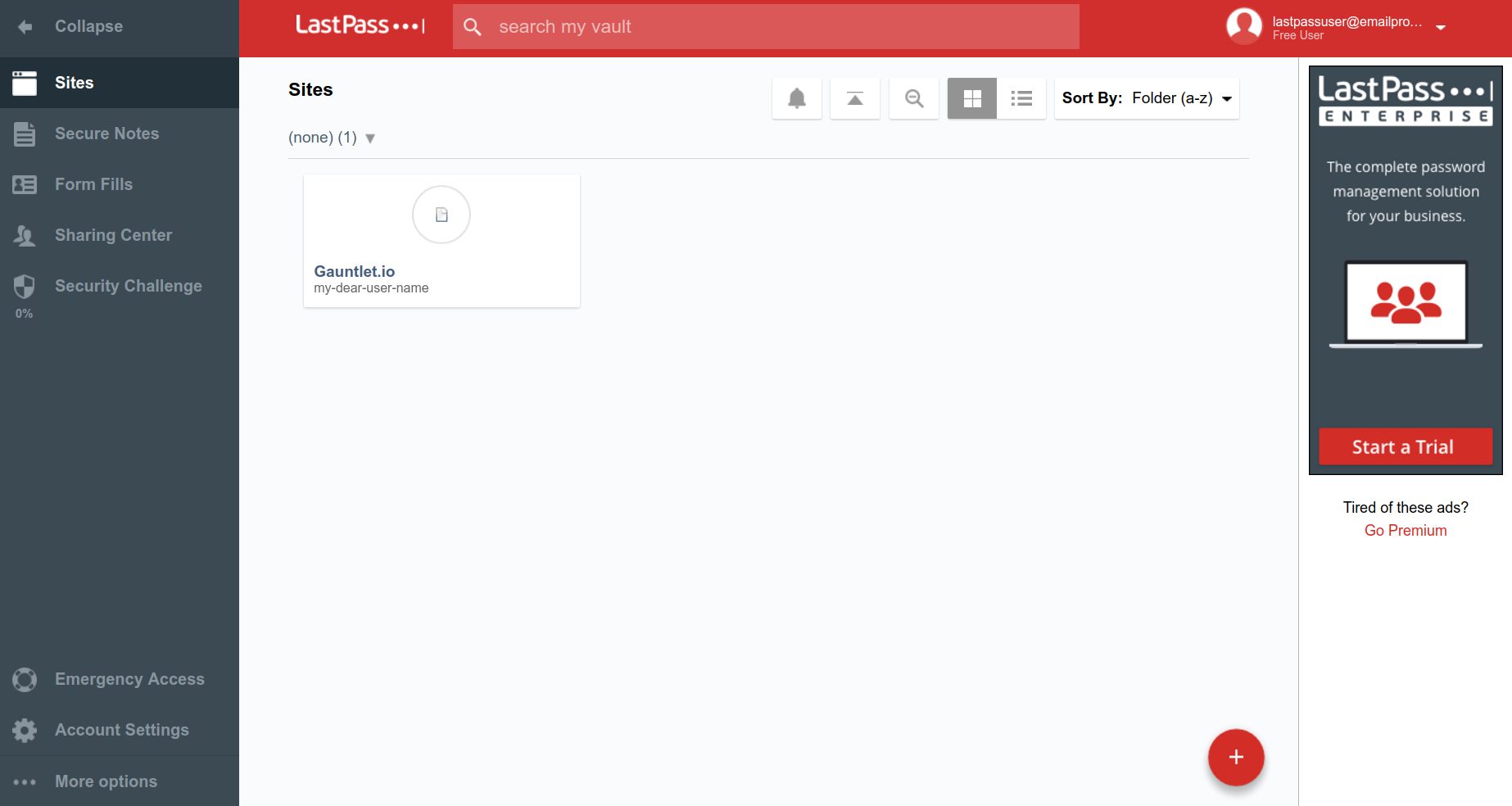
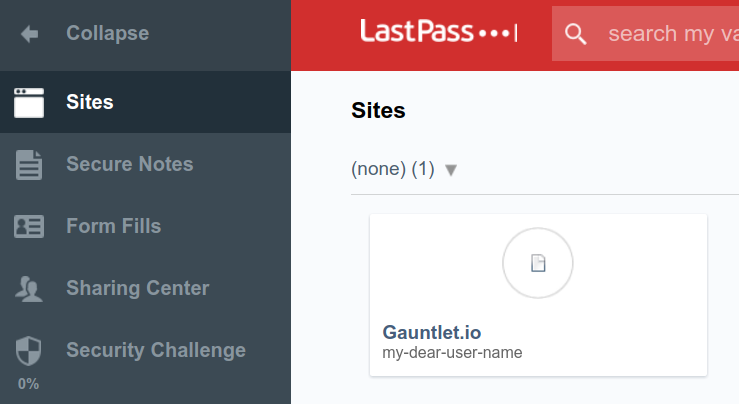
Then, I'm presented with the extension as a whole:
Let's discuss the security principles I've stated above:
1. Passwords must be complex: Doing it automated is better than doing it manually. We tend to stick to keyboard patterns instead of truly randomizing characters, let alone using special characters. Whenever you try to sign up, LastPass can generate a new password using default rules:
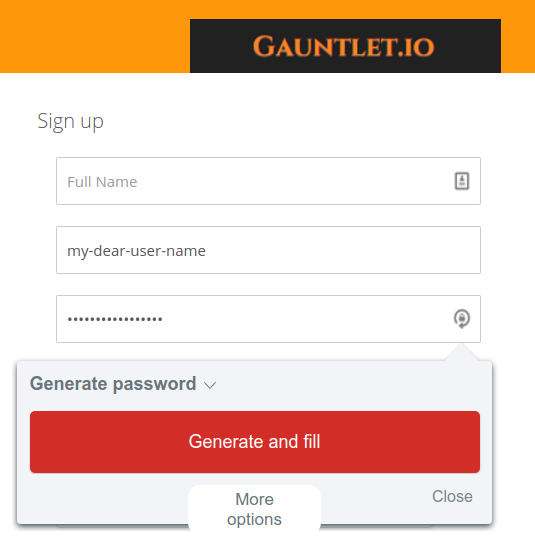
Or let you customize them by clicking on "More options":
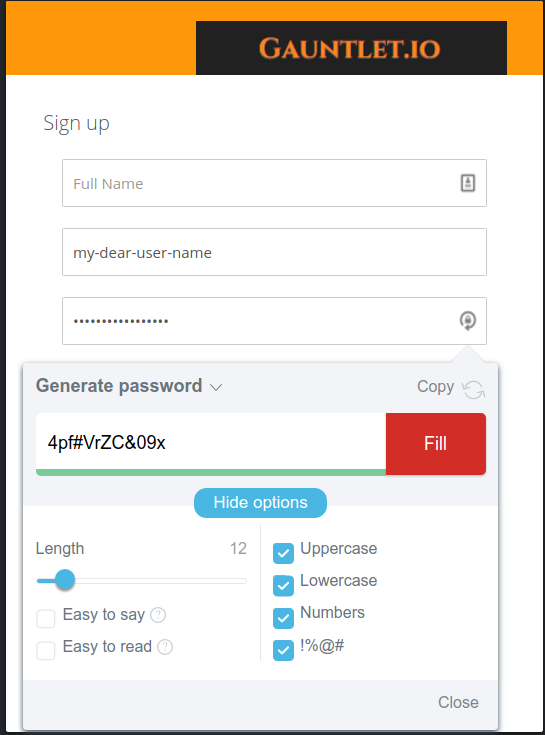
2. Passwords must be unique for every account you have: That's easily accomplished. The same password generation widget shows up in every password field. It's possible to identify password fields because they are input tags with the type="password" attribute.
3. Passwords must be stored securely: Easier said than done. The LastPass extension creates your "vault," a file containing your passwords that is encrypted using your master password (the password defined during the sign-up process). Actually, that should be the logic, but it's much more complex than that. Why is that the case?
Well, password managers are only decently secure when you can't decrypt a vault if you have compromised the client's device. But users may forget their master password, thus losing the master password means losing all other passwords as well. That said, instead of relying on the user's master password to decrypt the vault, wouldn't it be better to store the decrypt password in LastPass's servers and send it back to the device only when the user's email/password matches? Yes, it's better. Actually, they don't need to store the whole key, but part of it. This concept is called dual custody.
Ok, now in this scenario, the security of your vault lies on LastPass's servers. Is that a good thing? It depends! At least until November 17th, it wasn't.
But there is one worrisome thing: vault synchronization across devices.
It can only be done if the vault is stored on the server. It means that hacking LastPass should leak your vault and your vault key. These items may be separated in different servers, but it's hard to offer "device sync" and "forgot master password" functionality altogether. That's not necessarily how LastPass is designed. I didn't research it, but I have doubts about their implementation given the information presented in the previously linked article.
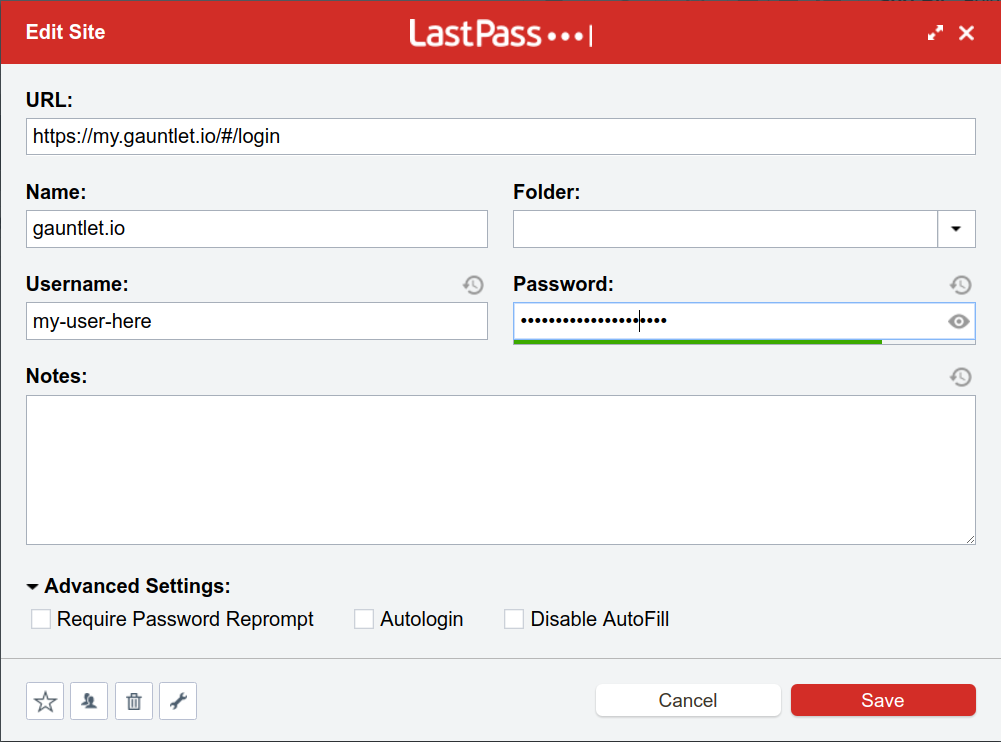
4. Passwords must be transmitted securely: In the case of LastPass, by default, the username and password are auto-filled thanks to the browser extension. It detects the current URL (the text in the address bar), looks for matches within your password vault, and automatically fills both fields:
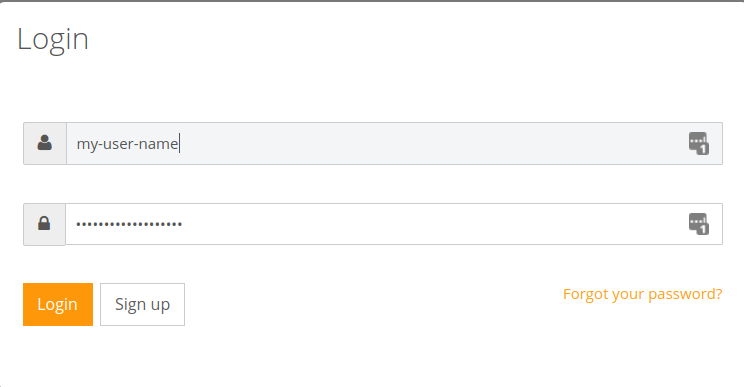
There are LastPass icons on the right. If you click on them, you'll be offered an option to choose "Log in as another user," in case you have more users for that website. In my case, I have only one, thus the "1" value near those icons.
But is it a safe password transmission from the vault to the website?
In this case, there is no need to copy/paste unless you disable autofill, thus preventing attacks on the clipboard. On the other hand, if the autofill extension is not secure, an attacker could craft a malicious URL to spoof a valid website and make the extension retrieve all credentials. This has actually occurred recently and in the past using XSS vulnerabilities on a page in a domain and iframing the login page to leverage the Same Origin Policy (SOP) to access the value of the password field.
5. The process of managing passwords must be easy to use: it's dead simple. It's been made for laymen, after all. After signing up for a website, you can manage every stored credential:
And then launch the website to authenticate directly:
They even offer a feature named "Security Challenge" that tests all your passwords against 'already leaked passwords,' 'weak passwords,' and much more:
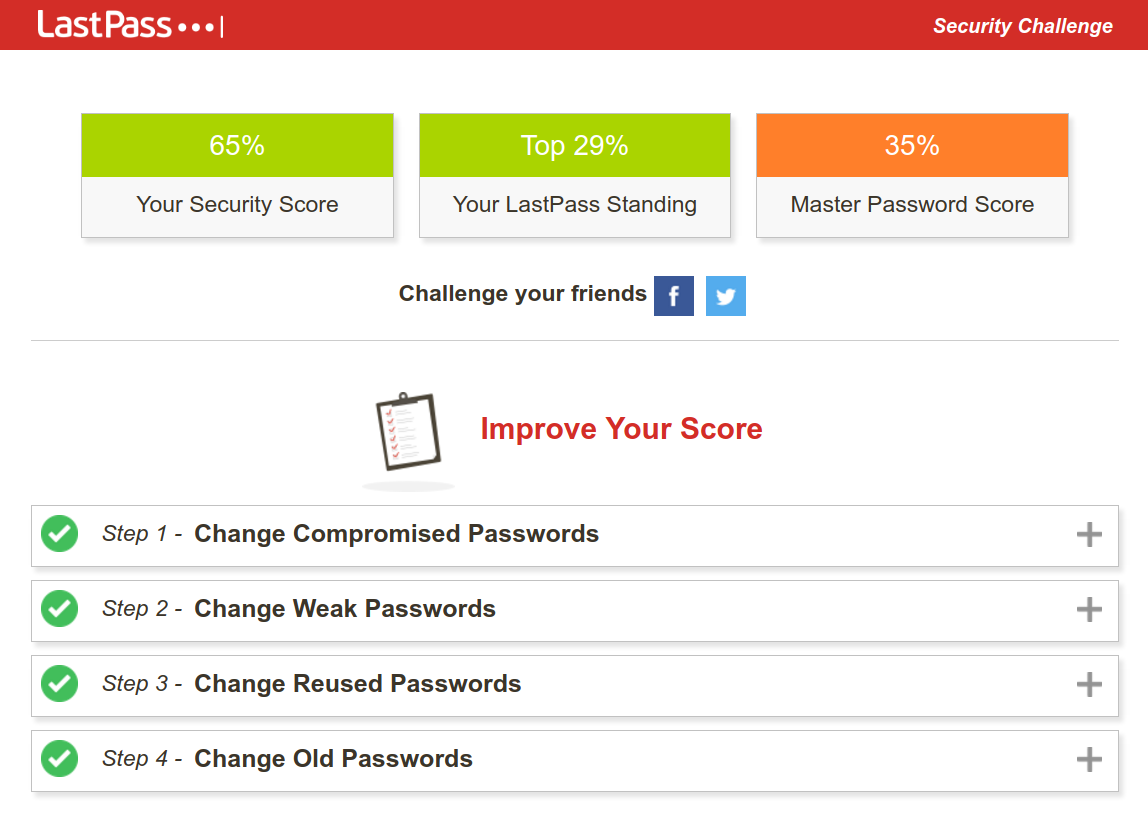
As it was my first account on LastPass and at least at first, I don't want to use it, I put a ridiculous master password hehe.
Offline Password Manager
For this topic, I'll use KeePass, a free and open-source password manager. What saddens me is that it uses Wine instead of having a version designed specifically for Ubuntu, which makes the interface look like Windows 95. But let's do it.
Offline password managers tend to offer more security in exchange for a decreased user experience, e.g., device synchronization. Let's start by installing KeePass.
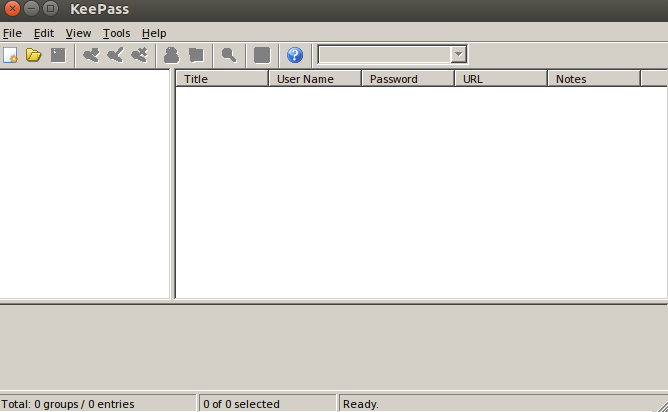
I tried to install the latest version (2.x), but only the classical version worked using Wine (1.x). Here's the first thing you'll see:
Let's proceed to create our vault. Note that it's possible to use a KEY to unlock our vault instead of a master password. Then, you should have this KEY file on a pen drive only. Actually, they name the combination of factors to unlock your vault the "composite master key." This combination of factors includes "(...) a password, a key file, a Windows user account key, and/or a key provided by a plugin (...)".
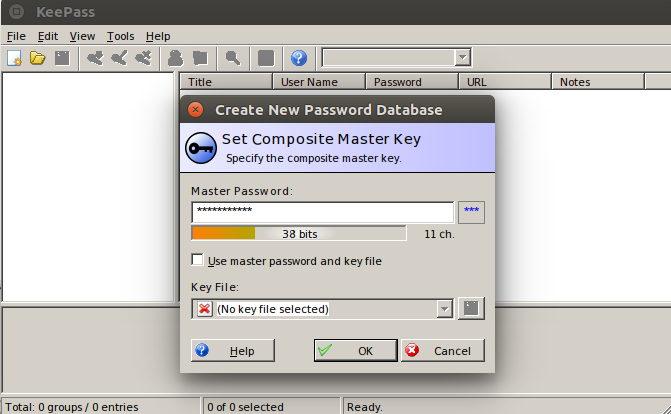
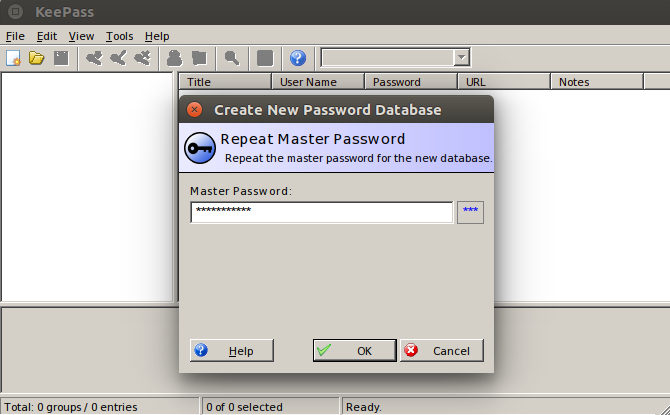
Then, repeat our master password:
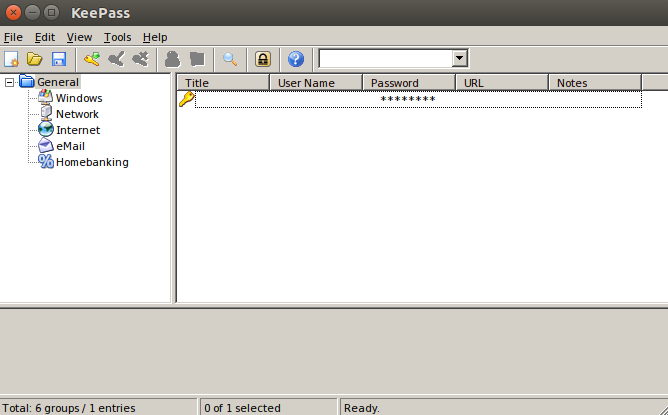
Now, a brand new world has appeared before us:
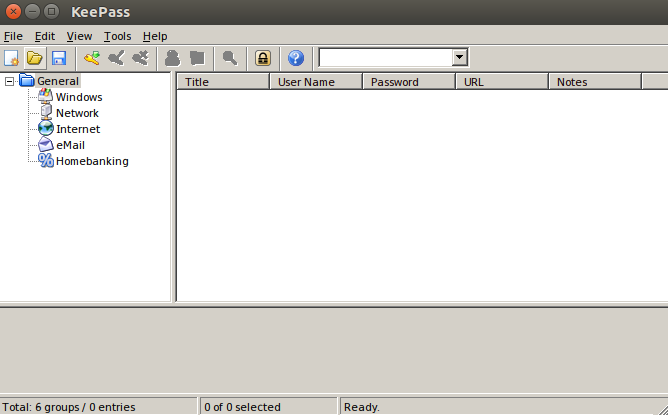
Let's dig into the details of each security principle:
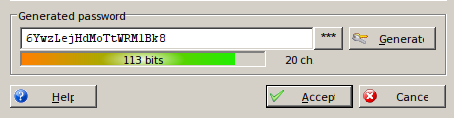
1. Passwords must be complex: This is accomplished by the "KeePass Random Password Generator," accessible through the menu "Tools -> Password Generator":
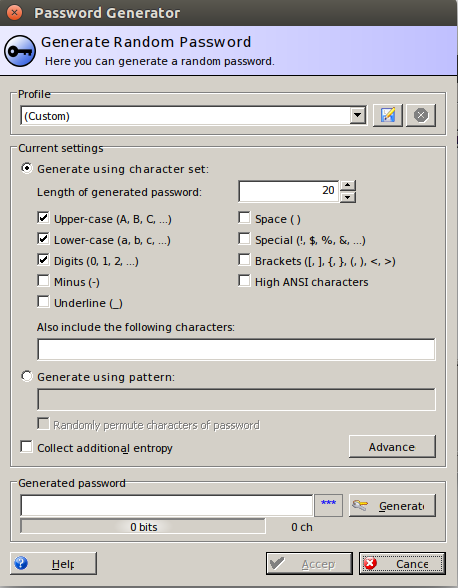
After clicking on "Generate":
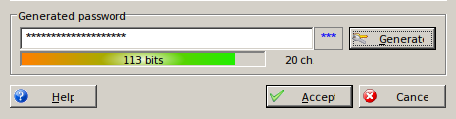
And in plain text:
Then, as we did not set a title, here's how it will look:
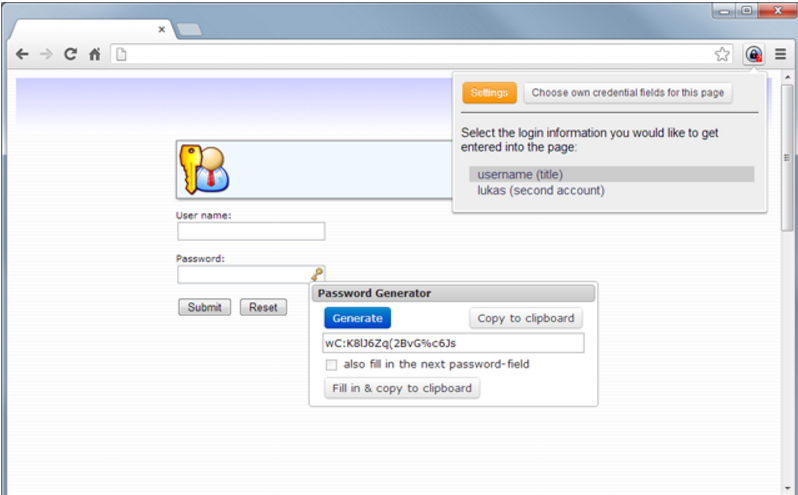
2. Passwords must be unique for every account you have: no secret here. You have to manually do this using the generator or use a browser extension to help you, accepting the risk that you're increasing the attack surface in exchange for more usability. KeePass has a lot of plugins, and it happens to have 2 plugins to work with Chrome: KeeForm and ChromeIPass.
Unfortunately, the KeepForm plugin for Chrome was removed, and it isn't present in the Chrome Web Store anymore, so we have to check ChromeIPass.
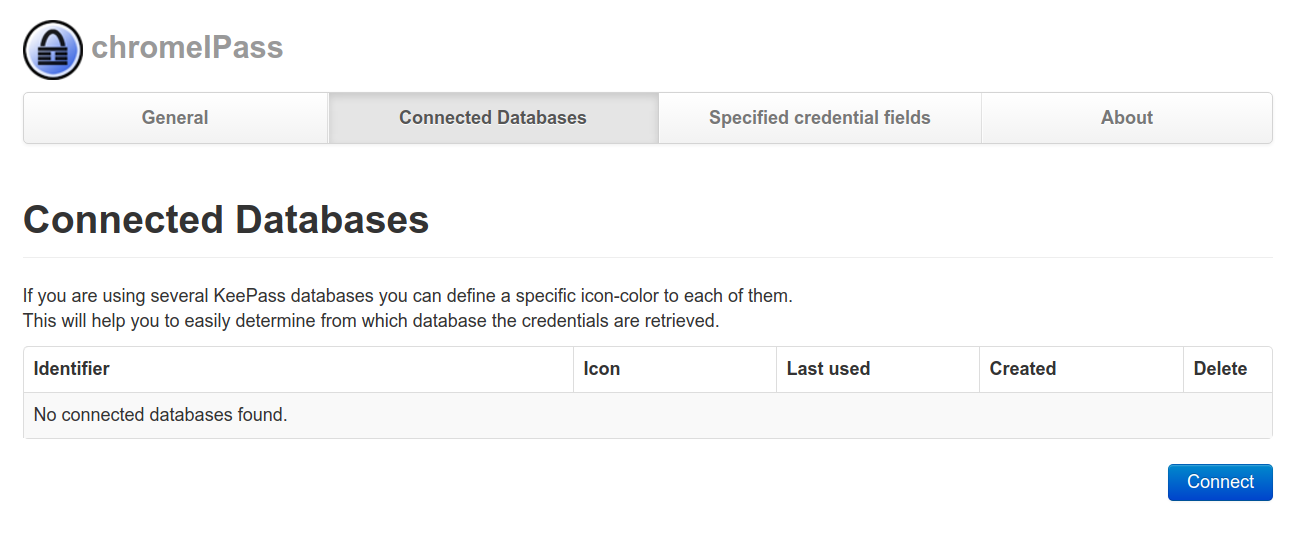
But it didn't work. I tried to set the "password database," but the "Connect" button simply doesn't work:
3. Passwords must be stored securely: This is, as always, a vast topic that we could dive into. However, in this case, it is as secure as it should be. You'll have an encrypted vault and only a master password or key file to decrypt it. No 'backdoors' or any other way to restore your master password/key as we saw with LastPass. Lose them, and you'll lose all your passwords. Neat.
4. Passwords must be transmitted securely: Copying and pasting, then clearing the clipboard after a few seconds is an acceptable way to transfer the password from the vault to your browser. Still, malware is a problem in this scenario.
5. The process of managing passwords must be easy to use: Not that convenient without a browser extension, but copying and pasting isn't that hard. And for mobile devices, you have to retype your password while looking at your password in plain text after you've opened your vault. Very similar to not using a password manager in this case.
High-Level Approaches Comparison
Everything with an asterisk (*) means "has strings attached that were discussed above."
| Feature | No PWM (Paper) | No PWM (Digital) | Online PWM | Offline PWM |
|---|---|---|---|---|
| Complex PW Generation Rules | Depends on User | Depends on User | X | X |
| Generate Unique Passwords per Account | X | X | X | X |
| Passwords are stored securely | X (*) | X (*) | X (*) | X |
| Passwords are transmitted securely | X (*) | X (*) | X (*) | X(*) |
| Shoulder Surfing Resistant | X | X | ||
| Server hacking resistant | X | X (*) | X | |
| Client hacking resistant | X | X (*) | X | |
| Robbery resistant | X | X | X |
Conclusion
Every option offers benefits and drawbacks. You're not necessarily crazy using paper (not a Post-it, please!), and you're not necessarily secure using the fanciest password manager either. The important thing here is to follow my 5 security principles.
But if someone comes to me and asks for the best option to start with, I'd suggest an offline password manager. If you really need to synchronize and so on, you can make your own vault sync or switch to an online password manager. If you know what you're doing, sync on your own. Otherwise, move to an online password manager.
I've been using the no password manager (digital) approach before the rise of password managers, and I'm considering switching to an absence of magic password manager. Ideally, open-source with few lines of code and trusted by the community. A security vault truly decrypted by a master password that only lies inside my mind and nothing else. Taking the risk of losing every password once I forgot the master password. That's what a good password manager looks like to me.
1Password is being recommended by some security folks, but it seems to work decently only on Mac. KeePass lacks the integration to have the same UX as LastPass on Ubuntu, at least, but I feel more secure using an offline password manager. LastPass worries me because of its many features that greatly increase the attack surface. Perhaps I should await for such tools to get more mature and provide a more user-friendly Linux version :)
See also
- Password Manager Vulnerabilities
- LastPass Remote Command Execution (RCE) vulnerability
- Even the LastPass Will be Stolen, Deal with It! [2015]
- How I made LastPass give me all your passwords [2016]
- Grab password with XSS [2014]
- The Emperor’s New Password Manager: Security Analysis of Web-based Password Managers [2014]
- Best Password Manager — For Windows, Linux, Mac, Android, iOS, and Enterprise [2016]
- Password Managers Compared: LastPass vs KeePass vs Dashlane vs 1Password
That's all for today.
Thank you.



